Archive For The “Internet” Category

In part 5 of “From ‘Content is King’ to Godlike,” we looked at methods and
What is Behavioral Economics?
Behavioral Economics is the study of human choice and decision-making. Unlike its classical economics predecessor, Behavioral Economics has two key divergences:
- Whereas classical economic theory assumes that both markets and consumers are rational actors, Behavioral Economics does not. In fact, BE practitioners demonstrate the irony of predictability in human’s behaving badly, or irrationally.
- Building from that point, BE has developed a series of scientific methods to test, measure, and yes, predict human irrationality.
- As the name somewhat suggests, BE bridges the academic disciplines of economics and psychology as well as other social sciences, neuroscience and even mathematics. That’s quite a lot.
- Incorporates Heuristics, i.e., humans make 95% of their decisions using mental shortcuts or rules of thumb.
- Incorporates Framing: The collection of anecdotes and stereotypes that make up the mental filters individuals rely on to understand and respond to events.
- Addresses market inefficiencies that classical economics does not, including
mis-pricing and non-rational decision making.
Behavioral Economics is a relatively new academic discipline whose roots go back to the 1960s largely from cognitive psychology. To many, Richard Thaler (Nobel Prize: 2017) is considered the father of BE. The University of Chicago professor has written six books on the subject.
Behavioral Economics Applications
While still considered a fledgling discipline, BE is growing rapidly, and arguably the most consequential new study area in academia. BE has already has been put to practical use in Marketing, Public Policy, and of course, AI, although its presence is rather opaque.
- PLAYING SPORTS
Principle: Hot-Hand Fallacy—the belief that a person who experiences success with a random event has a greater probability of further success in additional attempts.
Example: In basketball, when players are making shot after shot and feel like they have a “hot hand” and can’t miss.
Relation to BE: Human perception and judgment can be clouded by false signals. There is no “hot hand”—it’s just randomness and luck.
2. TAKING AN EXAM
Principle: Self-handicapping—a cognitive strategy where people avoid effort to prevent damage to self-esteem.
Example: In case she does poorly, a student tells her friends she barely reviewed for an exam even though she studied a lot.
Relation to BE: People put obstacles in their own paths (and make it harder for themselves) in order to manage future explanations for why they succeed or fail.
Learn more about Diane Israel. Also, see Diane Israel on LinkedIn.
3. GRABBING COFFEE
Principle: Anchoring—the process of planting a thought in a person’s mind that will later influence this person’s actions.
Example: Starbucks differentiated itself from Dunkin’ Donuts through their unique store ambiance and product names. This allowed the company to break the anchor of Dunkin’ prices and charge more.
Relation to BE: You can always expect a grande Starbucks hot coffee ($2.10) to cost more than a medium one from Dunkin ($1.89). Loyal Starbucks consumers are conditioned, and willing, to pay more even though the coffee is more or less the same
4. PLAYING SLOTS
Principle: Gambler’s Conceit—an erroneous belief that someone can stop a risky action while still engaging in it.
Example: When a gambler says “I can stop the game when I win” or “I can quit when I want to” at the roulette table or slot machine but doesn’t stop.
Relation to BE: Players are incentivized to keep playing while winning to continue their
5. TAKING WORK SUPPLIES
Principle: Rationalized Cheating—when individuals rationalize cheating so they do not think of themselves as cheaters or as bad people.
Example: A person is more likely to take pencils or a stapler home from work than the equivalent amount of money in cash.
Relation to BE: People rationalize their behavior by framing it as doing something (in this case, taking) rather than stealing. The willingness to cheat increases as people gain psychological distance from their actions.
These behavioral economics principles have major consequences on how we live our lives. By understanding the impact they have on our behavior, we can actively work to shape our own realities. As such, it’s becoming increasingly difficult, if not impossible, to decouple BE from AI, et al.
Diane Israel is a Chicago native and long-time supporter and advocate of the American Israel Public Affairs Committee (AIPAC). She is also famous for her culinary recipes. Diane can be reached at Diane@IsraelOnIsrael.com

In just a decade, the game-changing digital streaming and media service provider Spotify has transformed the music industry. The company’s popularity has marked the shift from physical to digital music and it has helped the world identify the internet as a key source for music distribution.
With more than 100 million subscribers since last year, Spotify is just one example of the impact of technology on the music industry. Today, the demand for digital music is stronger than ever and music tech startups, in Israel and elsewhere, have come out of the woodwork to effectively use digital technology to reshape and rejuvenate the music landscape.
This article was originally posted by NoCamels.com. See Featured article: Artificial Intelligence.
From creating different guitar sound effects with the use of one wireless touchpad to viscerally “feeling the music” with the aid of potent haptics on a chest strap, tech has brought benefits to both musicians and the people who listen to it.
NoCamels highlights four startups from Israel that are revolutionizing the music scene.
JoyTunes
With an ongoing health crisis lurking in the background, and much of the population staying at home, it might be the right time to pick up a new hobby — like learning to play a musical instrument. Learning to play the piano could be a logical first step and for that, there is Tel Aviv-based startup JoyTunes.
This music learning app uses educational methods, sound recognition, and their own patented MusicSense Engine technology to “reinvent the way to learn, play, and experience music.”
RevPad
Electric guitarists are known for their electrifying guitar solos at raucous rock concerts, which are often enhanced by extensive sound effects produced by effects pedals. Using a mess of cables, most musicians connect their guitars to several pedals, which they set on throughout the performance for desired effects.
Since Israeli startup GTC Sound Innovation’s revolutionary RevPad continues to free guitarists from these cumbersome pedals. The unique wireless touchpad controller is designed to attach easily to any amplified instrument and play a number of sound effects.
“Every guitarist has effects that he uses,” says Oded Elbonim, GTC’s sales and marketing director. “If it’s distortion, if it’s echo, if it’s tremolo, if it’s harmonizer, if it’s any kind of silly pedal that sits on the pedalboard on the floor. I’m sure you’ve been to concerts before, where you’ve seen the guitar player sometimes bending down and quickening and always having to go back to his place at the right time,”
JoyTunes’ apps use their MusicSense Engine tech to acoustically listen to notes that are being played by users in order to recognize and respond to them with feedback in real-time. According to the company’s founder Yuval Kaminka, this is what differentiates the startup’s apps from others on the market.
Woojer
A US-Israeli startup founded in 2011 has developed unique polyphonic “haptic technology” that enhances music and audio to literally let you feel sounds.
woojer strap
A user wearing the Woojer strap. Courtesy.
In other words, the wearable devices, which be worn as a strap or vest — not headphones, can accurately reproduce bass frequencies to deliver the emotional tactile sensation directly to the wearer’s body, the company has said.
“We have our own patented components that give you those haptic sensations to very accurately reproduce the same experience that even a deaf person will experience when they go to a concert or a theater,” says Kfir Bar-Levav, co-founder and CEO at Woojer.
According to Bar-Levav, Woojer’s tech takes the low frequency of any sound and translate it into a vibration that is felt by the body.
woojer vest
At the end of last year, the company ran an Indiegogo campaign where it raised over $4 million by more than 20,000 backers. It has already begun making deliveries of the product, though the campaign is still live, Bar-Levav said. The company also ran a Kickstarter campaign last year.
Woojer is also used to create immersive experiences in gaming and virtual reality.
The company has raised over $3 million to date.
“Users can in a few minutes play their first song with three notes, 20 minutes later play five notes, and in an hour and a half can play [the song] Jingle Bells in full,” he tells NoCamels.
“We improve pedagogy all the time,” he adds, “We look for those aha moments and milestones for users to realize how much they are learning.”
The company, founded in 2011, has more than 10 million users worldwide and is used by 10 percent of music teachers in the US. The company also works with music educators by combining teaching with new gaming features and technology.
Users can learn how to play through mobile apps featuring interactive listening, gaming features, and other music learning methodologies. Simply Piano, the company’s most recognized app, shows users which piano keys to press in order to play a song. Apps from JoyTunes are known for being interactive and teaching users to play intuitively.
The company says it has been chosen as one of the best apps by Apple and Google.
Last year, JoyTunes raised $25 million in a round led by Tel Aviv-based venture capital firm Qumra Capital. Other participants included New York-based venture capital and private equity firm Insight Venture Partners, an existing investor, venture capital fund Aleph and Jeremy Stoppelman, the CEO and founder of business directory service Yelp.
The company has raised a total of $43 million to date. Kaminka tells NoCamels the company strives to “reach evey single houshold ” and even become “the ‘Netflix for music learning.’
Emeo
Earlier this month, a Tel Aviv-based startup named Emeo announced the launch of its cutting-edge new product– the first digital practice horn for saxophone players.
The Emeo offers a unique solution to the problem faced by saxophone players, namely the loud sound made by the instrument and the difficulty in muting it, the company said.
The Emeo is a digital practice horn, that works like an electronic music keyboard, that you can connect to a computer. The digital horn allows musicians to play anytime and anywhere, via USB, MIDI, or Bluetooth connections to computers or smartphones.
The Emeo is a digital practice horn, known as a wind MIDI wind controller. It works like an electronic music keyboard, that you can connect to a computer. The difference between the Emeo and other MIDI wind controllers, is that it has the feeling of being a real saxophone.
“You play the Emeo through speakers or headphones, by connecting it via USB-MIDI or Bluetooth to DAW programs on computers, tablets and smartphones,” said Emeo’s marketing specialist Michael Simkin.
The company has also partnered with Imox’s Respiro, a new generation software synthesizer using physical modeling that contains a “state of the art” sound engine able to reproduce the sound and behavior similar to wind-instruments. The company has crafted a range of high-quality MIDI sounds especially for the Emeo, Simkin says.
When he was younger, the company’s co-founder Oleg Raskin, a professional saxophone player, faced complaints from family members and neighbors for the loud sound created by practicing the saxophone.
Diane Israel is a Chicago native and long-time supporter and advocate of the American Israel Public Affairs Committee (AIPAC). She is also famous for her culinary recipes. Diane can be reached at Diane@IsraelOnIsrael.com

Israel’s Amos-17 satellite by Ramat Gan-based company Spacecom was successfully launched into space overnight Wednesday in Cape Canaveral, Florida. The launch, aboard a SpaceX Falcon 9 rocket, came almost three years after a spectacular launchpad explosion destroyed Spacecom’s Amos-6 satellite and the SpaceX rocket it was on in September 2016.
This article originally appeared in NoCamels.com
AMOS-6 was then touted as Israel’s most advanced satellite, operated by Spacecom and developed with its partner, the Israel Aerospace Industries. Its goal was to beam free internet across sub-Saharan Africa as part of a project with Facebook. The tech giant had in 2015 launched Internet.org, a non-profit initiative that would bring together technology leaders, nonprofit organizations and local communities to provide Internet access to the most remote regions of the world.
The Amos-17, built by Boeing, will have much the same objective: to provide satellite communication services including broadband and high-speed data services to Africa as well as the Middle East and Europe.
The satellite was originally scheduled to be launched on Saturday but was delayed to fix a suspected faulty valve during tests.
Once operational, Amos-17 will be the most technologically advanced satellite over Africa, providing extensive C-Band HTS capabilities, Ka-Band and Ku-Band to a range of markets, and combining broad regional beams and high throughput spot beams to maximize throughput and spectral efficiency, Spacecom says.
Amos-17 will operate from 17° East to expand and strengthen Spacecom’s coverage of the growing satellite service markets in the continent which suffers from snail-pace internet speeds and inadequate infrastructure. According to a 2018 joint report by the World Wide Web Foundation, the Alliance for Affordable Internet, and UN Women, internet penetration across the continent stands at 22 percent.
Featured article on artificial intelligence.
To get connectivity via Amos-17, a simple solar-powered terminal is required, the Times of Israel reported citing remarks at a press conference last month by Eran Shapiro, director of business and technology ventures at Spacecom.
Spacecom says the Amos-17 “will be a state-of-the-art multi-band high-throughput satellite, utilizing Boeing’s advanced digital processor platform, that will provide reliable and flexible satellite solutions and offer a significant competitive advantage for our customers.”
The satellite’s “inherent flexibility of the digital platform with a mix of fixed and steerable beams ensures a fast response to changing customers’ needs.”
The $250 million Amos-17 is expected to operate for at least 20 years.
Diane Israel is a Chicago native and long-time supporter and advocate of the American Israel Public Affairs Committee (AIPAC). She is also famous for her culinary recipes. Diane can be reached at Diane@IsraelOnIsrael.com
Learn more about Diane Israel. Also, see Diane Israel on LinkedIn.
Tuberculosis (TB) is curable and preventable. But TB kills 1.6 million people a year (or 4,000 people a day) and is one of the top 10 causes of death worldwide, according to the World Health Organization.
The stigma and adhering to a treatment regime are key reasons this extremely infectious disease is still a risk.
According to the WHO, to beat TB, a patient must take four antimicrobial drugs for at least six months. But health officials across the globe say that without supervision and support, many TB patients will not finish their medications.
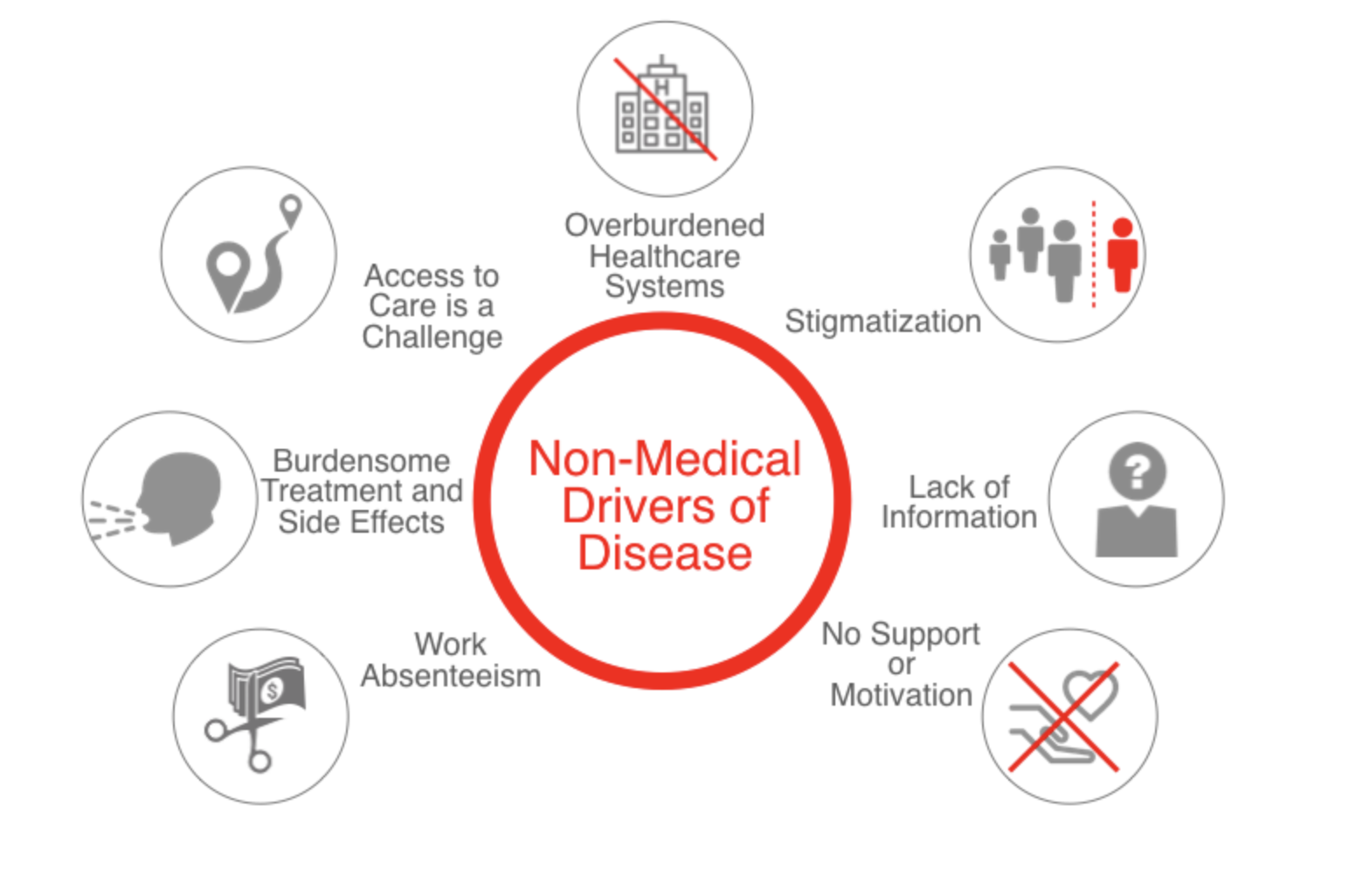
“Non-medical drivers of disease such as stigma, access to care challenges, burdensome treatment protocols, and a lack of information, motivation, and support make it difficult for patients to do the right thing and take their medication,” said Jon Rathauser, CEO and founder of Israeli digital health startup Keheala, in a statement on Thursday.
Keheala, a Tel Aviv-based startup with offices in Nairobi, Kenya is on a mission to improve healthcare access and treatment outcomes for patients.
This article was originally posted by NoCamels.com. Featured article: Artificial Intelligence.
Diane Israel is a Chicago native and long-time supporter and advocate of the American Israel Public Affairs Committee (AIPAC). She is also famous for her culinary recipes. Diane can be reached at Diane@IsraelOnIsrael.com
Learn more about Diane Israel. Also, see Diane Israel on LinkedIn.
First founded in 2014, Keheala developed a “low-tech” solution to help motivate treatment adherence and get patients to take their medications on time, using basic phone features – like SMS or text – and behavioral science strategies for a platform based on USSD – unstructured supplementary service data.
“This means patients can dial in (*694# in Kenya) and text Keheala,” Rathauser tells NoCamels. Shortcodes are available on 99 percent of basic feature phones. The platform securely delivers reminders, disease information and enable self-verification of treatment, simplifying and informing the process of care.
Here’s how it works: The program sends text messages to patients to take their meds on time. If the patient takes his meds, he sends a text back saying so and will get another message of thanks. If he doesn’t respond, more text messages are sent, followed by phone calls from Keheala supporters to verify adherence.
“They can receive a ‘push’ via SMS with reminders to take their meds, and they can self-verify that they took it, as well as connect with supporters and mentors,” says Rathauser, who is originally from New Jersey and holds public health and business degrees from McGill University and the Technion Institute. For example, if the system recognizes that there has been no activity or ‘check-in,’ “a mentor can initiate a text conversation and ask how the person is doing and if they need anything.”

With frequent high-profile reports of sites, or even entire networks (Amazon AWS 2017) being shut down by hackers, it does beg the question: Can a hacker shut down the entire Internet? After all, if you can shut down Amazon, the CIA, or Twitter, could not a more wide scale, total blackout of the Internet be a reality?
Answer: Not really, and here’s why.
The Internet was designed to be resilient. In fact, the first vestiges of the Internet go back to the 1960s and the ARPANET and later DARPANET projects commissioned by the U.S. Defense Department. The initial objective was to develop a network of computers that could survive a nuclear attack. As such, redundancy was no afterthought. It was aforethought. Today this interconnectivity exists as the TCP-IP (Transmission Control Protocol – Internet Protocol), commonly known to today as simply the IP protocol.
All said, there are three areas where the Internet is vulnerable. The first one is rather recent, about ten years old. The Cloud. When Amazon AWS was shut down for nearly a day back in 2017, all its customers, primarily small businesses, but not all so small, who decided to put all their web services on AWS, went down too.
Tier-One ISP Backbone is where we are most vulnerable.
There are tens of thousands of ISPs (Internet Service Providers) out there but only a handful provide the backbone of Internet connectivity. In fact, most of the smaller ones are reselling services they purchase and rebrand as their own, typically from a bigger fish that makes their money from volume. Nothing new here.
But the big boys like AT&T, Comcast, Level 3 and Verizon are so vast in the amount of traffic that goes through them that if just one of them went down, 20 to 40 percent of the Internet would go down with them. And nobody really knows if the stress on the other backbone providers would provide a domino effect. So at least theoretically, the Internet could go down for a brief period. But theoretically only. These backbone providers invest billions each year to maintain and upgrade their resilience and redundancy. Actually, these backbone are probably the most redundant systems the world has ever seen. Arguably, not even the Space Shuttle had as much redundancy. So while theoretically possible, the bigger concern is hackers actually hacking their way inside the backbone. No one has ever succeeded in doing that. You’d probably have a better chance of hacking the CIA’s site than you would one of these backbones. The reason is that these companies all preceded the Internet as telecommunications backbones back when telephony was our most treasured and sophisticated communications network. In other words, our backbone providers have decades of experience in providing the most robust security standards, some of which will likely never be made public.
DNS Disruption.
Aside from site hacking whereby one website is compromised due to a deliberate hack of that site, systemic outages either originate from cloud hacking or DNS (domain name service) hacking. DNS providers are basically the folks who manage where your domain points to. In other words, if you own thisismycompany.com, you must tell the DNS where that domain is hosted via IP. So the DNS not only knows your domain name but also tells all other computers the IP (or computer address) where it can actually be found. For fun, you can actually find a website by typing in its IP address only without the actual domain name. What this means is that if a hacker can mess with the IP address it can become a major nuisance, in effect, making your site unreachable while at the same time it is technically functioning. A bizarre state where your Internet browser cannot resolve the multiple redirects that the hacker assigned to say a cloud, like what happened when Amazon AWS went down.
Okay. So a complete shutdown of the Internet is not likely, just like a complete shutdown of our entire power grid. But put that into perspective. Remember when New York City lost power for several days back in the late 70s? Such a moment is a cautionary tale of how we need not a global shutdown of the Internet to be catastrophically impacted. Just imagine if New York City’s Internet went down even for a day. Everything would come to a screeching halt, not just electrical power. Everything. Banking, Gas stations, grocery stores. And if you don’t have a full tank of gas you wouldn’t be driving anywhere either. So despite the Internet’s truly global reach, a localized complete outage would all-encompassing. As a civilization, we have never been so dependable on technology as we are right now. All previous “blackouts” are not adequate comparisons for this very reason. As such, it wouldn’t hurt to have some extra food and water around at the very least.
Diane Israel is a Chicago native and long-time supporter and advocate of the American Israel Public Affairs Committee (AIPAC). She is also famous for her culinary recipes. Diane can be reached at Diane@IsraelOnIsrael.com

My recent article, “Internet Apocalypse?” lays out the three most vulnerable points of attack that could potentially shut down the entire Internet, and how any such catastrophe would likely not be global but rather localized to a city or region, which is not to say that such a containment would not still be a total failure. What follows is an excerpt from a recent story published by NoCamels.com with Israeli Prime Minister Benjamin Netanyahu setting the stage.
“Ladies and gentlemen,” the robotic voice said, “this conference has just been hacked. Ironic, isn’t it? A conference dedicated to cybersecurity being hacked.”
“We are based in a country not far from Israel. That’s all you need to know for now. The bank accounts of everyone sitting in this hall have just been frozen. The intellectual property of your companies is in our hands, so are your private conversations. This information is being sent to your competition and your enemies,” it went on.
It was the fourth day of the 8th annual 2018 Cyber Week conference at Tel Aviv University, a global event gathering leading cybersecurity researchers, entrepreneurs, and insiders, began with a threat.
Israeli Prime Minister Benjamin Netanyahu, a main speaker at the five-day event, took to the stage on Wednesday and aired an audio clip announcing a large-scale hack to an audience of some 8,000 attendees from 85 countries.
The threat was not real; Netanyahu was simply trying to drive home a point. “This is not far-fetched,” he said, warning that hackers and state-backed actors “can do everything that you heard here and much more.”
“Hackers can cripple our most sensitive systems. They can even take over, literally take over, some of those vital systems. And it is not something that is theoretical in the future. It’s already happening in the present, as you well know. You wouldn’t be here. You wouldn’t have companies. There wouldn’t be this thriving business if there wasn’t this amazing threat to our banks, our airplanes, even our weapons,” Netanyahu said.
“This is a supreme test for our civilization. It is going to be tested not only by criminal organizations, by terrorists, but by other states,” he said. “This is why we’re holding this cyber conference here. It is to protect the present and ensure the future, no less than that.”
Netanyahu also praised the cybersecurity ecosystem in Israel, saying the country is “punching at 200 times above our weight here.”

My sister, whose political slant is irrelevant, has a common lament. “Who can you believe these days?” Indeed, those days where 90 percent of news consumption was provided by the Big 3 (ABC, NBC, and CBS) evening news programs are so far in the past that the younger generations have no reference to objective reporting in that tradition. Back in those days, a reporter had an honorable and now bygone standard.
If your reporting showed your political bias then you are not doing your job.
My how things have changed. Today, those days of Walter Kronkite (and anchors like him) where the principal message was the facts has almost completely eroded into advocacy journalism. On the extreme side of this, which ironically has gone mainstream (it’s very confusing), an entire network — FoxNews — no longer even pretends to be objective. Yet, at the same time, its audience still thinks they are getting objective journalism. In fact, so overt is FoxNew’s alignment to the Trump administration that the likes of Sean Hannity act as a shadow “chief of staff” to the president, meeting and advising him sometimes daily while, at the same time, reporting on matters in which he is directly involved and clearly influencing. How anyone can call this journalism is beyond me. But this is the era we live in.
Featured article: Artificial Intelligence.
On the other side of the mainstream spectrum, the legacy of Kronkite survives (albeit as an endangered species) through the dry and unemotional delivery of the Mr. Spock-like Wolf Blitzer. How do we know this? As yourself the same question journalists used to ask themselves. Can you identify Blitzer’s politics by the way he reports? Not really.
Between Hannity and Blitzer is filled-in with right-leaning advocacy journalism, although CNN is still considered centrist (only slightly to the left of center) whereas MSNBC is clearly left-of-center and undeniably advocating for the left.
But political slant is one thing. Getting to the truth, however, is often transcendant of political bias. After all, like my sister, honest seekers of the truth are still out there searching for the facts. Fortunately, FactCheck.org has provided a helpful guide (video) for bringing skepticism to your news consumption, and how to avoid spreading it.
The bottom line is this. Make sure you are getting news that is actually real. From there, choose your poison.
Diane Israel is a Chicago native and long-time supporter and advocate of the American Israel Public Affairs Committee (AIPAC). She is also famous for her culinary recipes. Diane can be reached at Diane@IsraelOnIsrael.com

The history of computing has been largely a tale of developing amazing applications for which processing speeds were insufficient to make these innovations practical. In other words, the adage that “content is King” is only the case because of speed bottlenecks. But with 5G (fifth generation wireless technology) on the horizon, we may be on the verge of a new Monarchy. The Speed King.
Segments from the following were originally published by NoCamels.com.
What is 5G?
Fifth-generation wireless, or 5G, is the latest iteration of cellular technology, engineered to greatly increase the speed and responsiveness of wireless networks. With 5G, data transmitted over wireless broadband connections could travel at rates as high as 20 Gbps by some estimates — exceeding wireline network speeds — as well as offer latency of 1 ms or lower for uses that require real-time feedback. 5G will also enable a sharp increase in the amount of data transmitted over wireless systems due to more available bandwidth and advanced antenna technology. Thirty to fifty times fast than 4G. The impact will be revolutionary, making home appliances smart, surgical robots even smarter and more precise, drones ubiquitous and artificial intelligence downright scary!
Intel’s history
American PCU processing giant Intel dominates the PC and server processor market, netting about 80 percent of the market worldwide. But as far as the mobile revolution is concerned, Intel missed the boat. Previous attempts to enter the smartphone market have been mediocre at best. But it has had considerable success in entering the mobile market. And with 5G it plans to go from player to dominator. The company is in a transition, adopting a data-centric model that is all about 5G.
And Intel’s Israel operations are playing a key role in the overhaul. This means that its innovative products, already ubiquitous, will be even more so. “New hardware will basically be in all aspects: data collection by new sensors (e.g. Mobileye), communication (e.g 5G), computing (e.g artificial intelligence),” Ben Sinai says. An ambitious move into the mobile phone market is also in the offing, as it is “certainly an ingredient” in Intel’s wider vision.
And Intel Israel, he says, is a “very important design center of Intel Corporation, leading some of its strategic developments in the area of computing, communication, security and more.”
Automotive and cybersecurity
Intel also has another edge. Last year, the company acquired the Jerusalem-based Mobileye, a developer of cutting-edge autonomous driving technologies, for a whopping $15.3 billion. Mobileye is considered a leader in advanced driver assistance systems – including pedestrian detection, collision warning – aimed to prevent road collisions. The acquisition marked Intel’s entry into the vibrant automotive market, and the industry plays a central role in Intel’s vision for the future.
“Autonomous cars will need constant, fast communications, they will move in sync on their own network,” Ben Sinai says, envisioning a future with zero accidents, a better environment due to expected reduced car ownership, and a transformed transportation industry which he says will have to adjust to accommodate self-driving cars.
As for the potential dangers posed by mass connectivity, Intel, he says, “is always thinking about security, and established a division at the Intel management level dedicated to looking for breaches and vulnerabilities.”
The bottom line is this. Intel now sees how IoT (Internet of Things) is redefining what the end device looks like. It’s no longer just a computer or a smartphone, and intends to have its technology in all these things, pun intended.
Diane Israel is a Chicago native and long-time supporter and advocate of the American Israel Public Affairs Committee (AIPAC). She is also famous for her culinary recipes. Diane can be reached at Diane@IsraelOnIsrael.com
